Cybersecurity is just another of a long list of things that entrepreneurs and small businesses wish they didn’t have to think about. However, in this case, what you don’t know really can hurt you.
Cybersecurity is just another of a long list of things that entrepreneurs and small businesses wish they didn’t have to think about. However, in this case, what you don’t know really can hurt you.
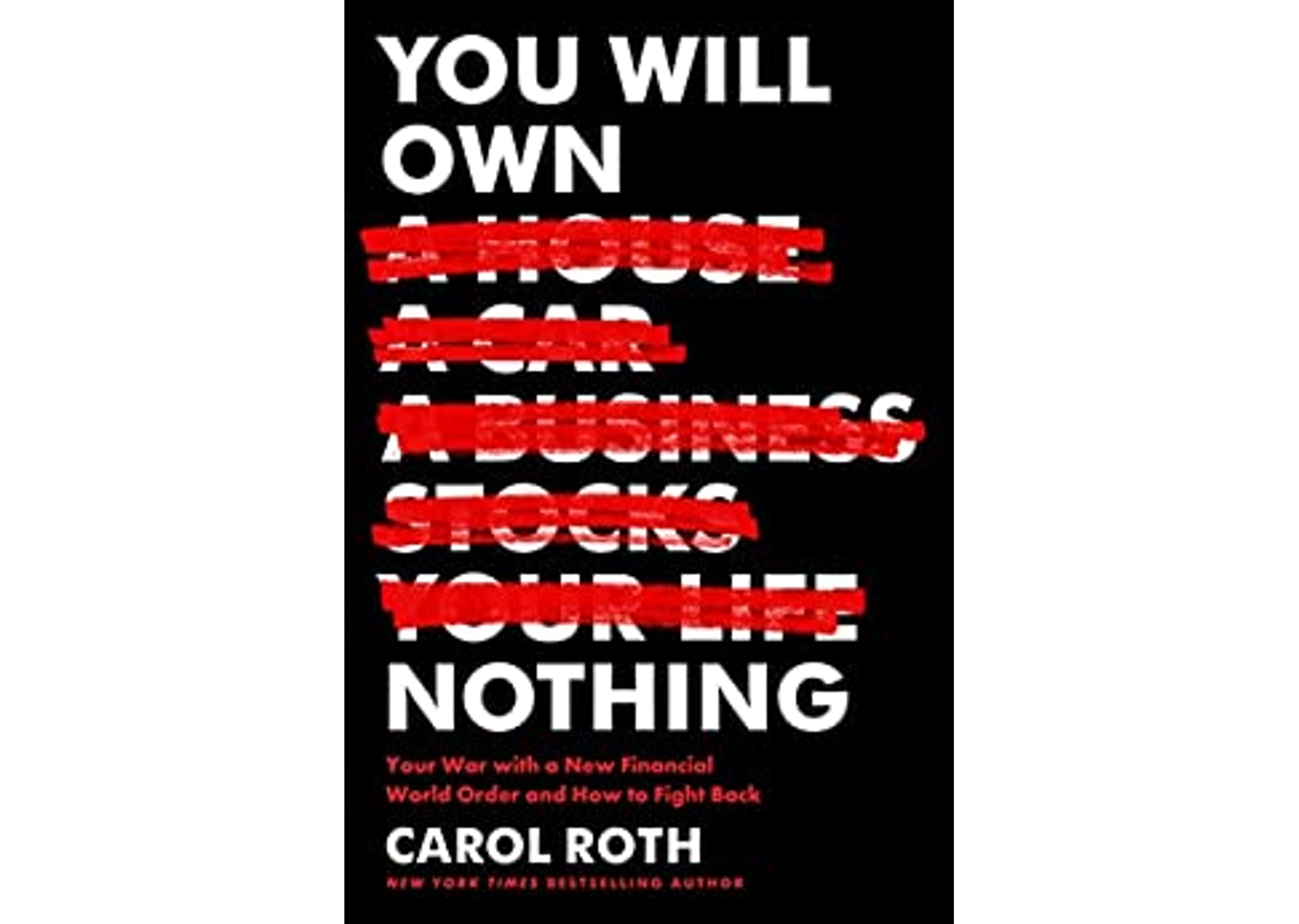
Carol tries to prioritize and simplify cybersecurity concepts in her recent post on MasterCardBiz, “Cybersecurity: 5 Risks Small Businesses Need to Understand.” Carol begins:
“Why would anyone want to steal your company’s data? Security expert and CEO of Kalki Consulting Vikas Bhatia says, “Every small business has, or is connected to others that have data worth stealing.”
You may have read stories about a disgruntled employee trying to cause havoc, but Bhatia believes almost all cybercrime is financially motivated.
In order to better protect yourself and your business from the chaos of a cybersecurity breach, let’s examine five of the top cybersecurity risks for small businesses.
Don’t Put Your Head in the Sand – Get an Assessment of Your Risks
Maybe you’ve “got a guy” (or gal) who helps you with your IT issues. They may be truly competent and helpful, but don’t assume that they are pros at security. They may have a basic knowledge, but Bhatia stresses, “IT pros and security pros are two different types of people.”
But what is the real value of an IT assessment? Bhatia says, “Without an independent lens to view cyber threats through, your security could be compromised.”
This sentiment is echoed by Tia Ung, president of Root Port LLC, a company that provides full IT support. Ung says, “Devastating security threats can end businesses. An IT security assessment helps you avoid becoming the next victim.”
Protect PII – Keep Personal Data Personal
If you don’t know what PII is, I can assure you that your company has some (or a lot!) of personally identifiable information (PII) in customer databases, etc. Home phone number or cell phone number, email address, home address – all PII data.
Then, of course, if you pay any employees or contractors, you probably have access to their social security numbers and possibly their bank accounts.”
You can read the rest of the post here.